This case study documents structural inconsistencies discovered in an Amazon API endpoint responsible for updating a child profile.
The analysis was performed using a single captured browser request and executed through Rentgen without manual scripting or custom configuration. Total execution time: approximately 2 minutes.
Endpoint under test
PUT https://data.amazon.com/custom/profilepickerserviceapicontracts/marketplaces/{id}/members/{memberId}
Use case: update the name field of a child account profile.
No complex workflow. No transactional logic. A minimal update scenario.
Why this matters
API contract consistency is critical in distributed systems. Incorrect status codes, edge-layer interference, and improper request validation create operational friction long before they create visible failures.
The findings below are not security exploits. They are structural API hygiene signals.
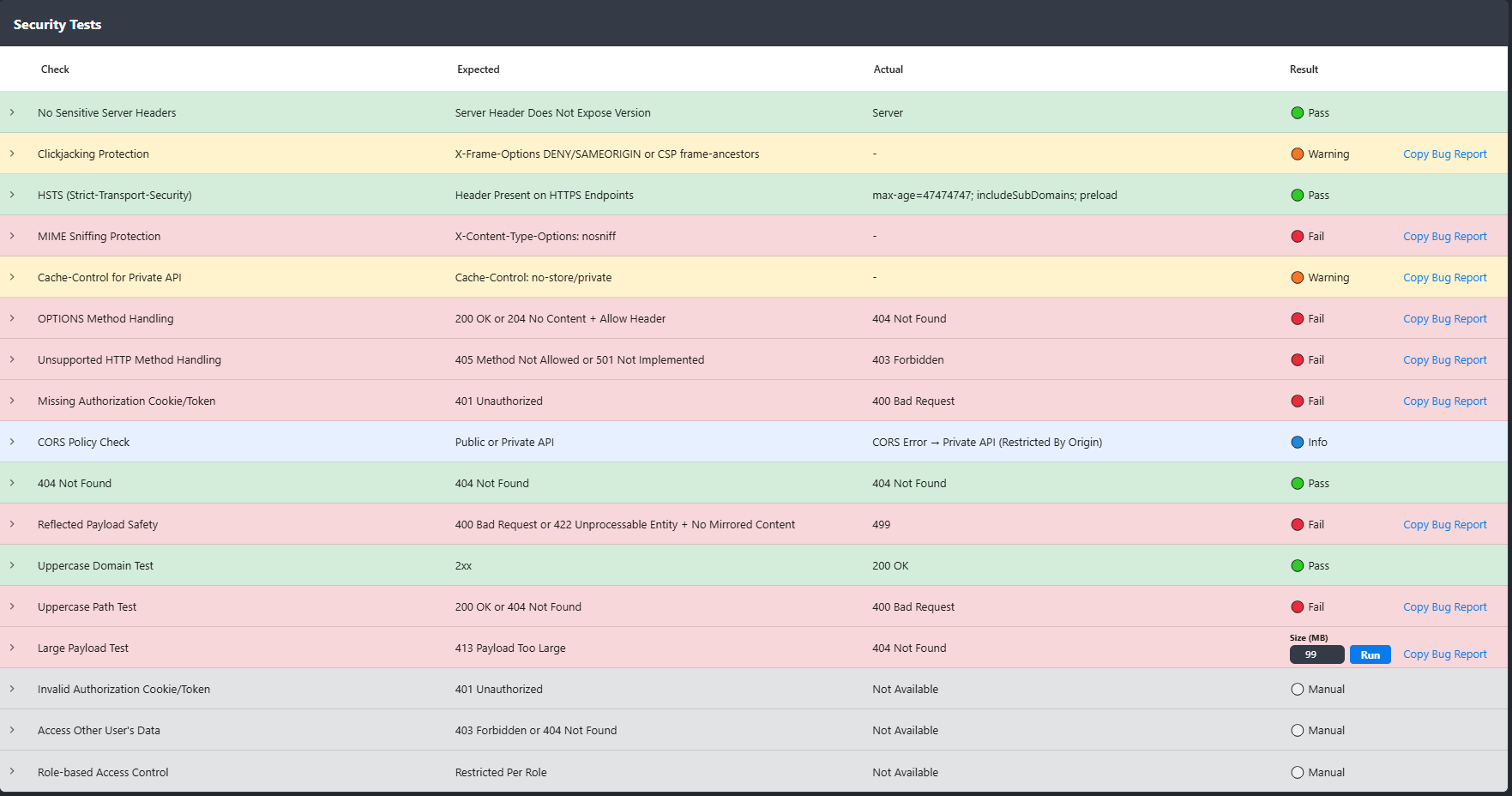
1. Authorization handling inconsistency
When authentication tokens were removed, the expected response was: 401 Unauthorized.
Actual response: 400 Bad Request with a generic message:
{
"message": "Sorry, We are experiencing issues right now."
}
This introduces semantic ambiguity. A 400 response suggests malformed input, while the actual failure condition is missing authentication. Such mismatches complicate debugging and monitoring logic.
2. Reflected payload safety and CDN interference
Injecting JavaScript content in the request body should produce a structured 4xx validation response.
Instead, the endpoint returned 499, a non-standard status associated with CDN behavior.
When edge infrastructure modifies or replaces API responses, the contract becomes unpredictable for client applications.
3. Uppercase path variation returning HTML
Converting the request path to uppercase should result in:
404 Not Found or normalization.
Instead, the response was: 400 Bad Request with a full HTML error page originating from CloudFront default configuration.
A JSON API returning HTML breaks strict client parsers and indicates incomplete edge error handling configuration.
4. Unsupported HTTP method returns 403
Expected:
405 Method Not Allowed or 501 Not Implemented.
Actual: 403 Forbidden.
A 403 response implies permission constraints rather than unsupported method semantics, leading to incorrect debugging assumptions.
5. OPTIONS request inconsistency
The OPTIONS method should return:
200 OK or 204 No Content with an Allow header.
Instead, the API returned 404 Not Found, despite the same route functioning correctly with PUT.
This indicates incomplete route method handling.
6. Large payload handling
A ~10MB payload was sent to test request size validation. Expected behavior: 413 Payload Too Large (early rejection).
Actual behavior: prolonged processing followed by 404 Not Found.
This suggests that request validation occurs too late in the processing chain, increasing resource consumption risk.
Additional header observations
- Missing
Cache-Control: no-store/privatefor a private API. - Missing
X-Content-Type-Options: nosniff. - No explicit clickjacking protection headers (low impact for JSON but recommended).
These are minor hygiene gaps but contribute to overall contract robustness.
Rentgen certificate result
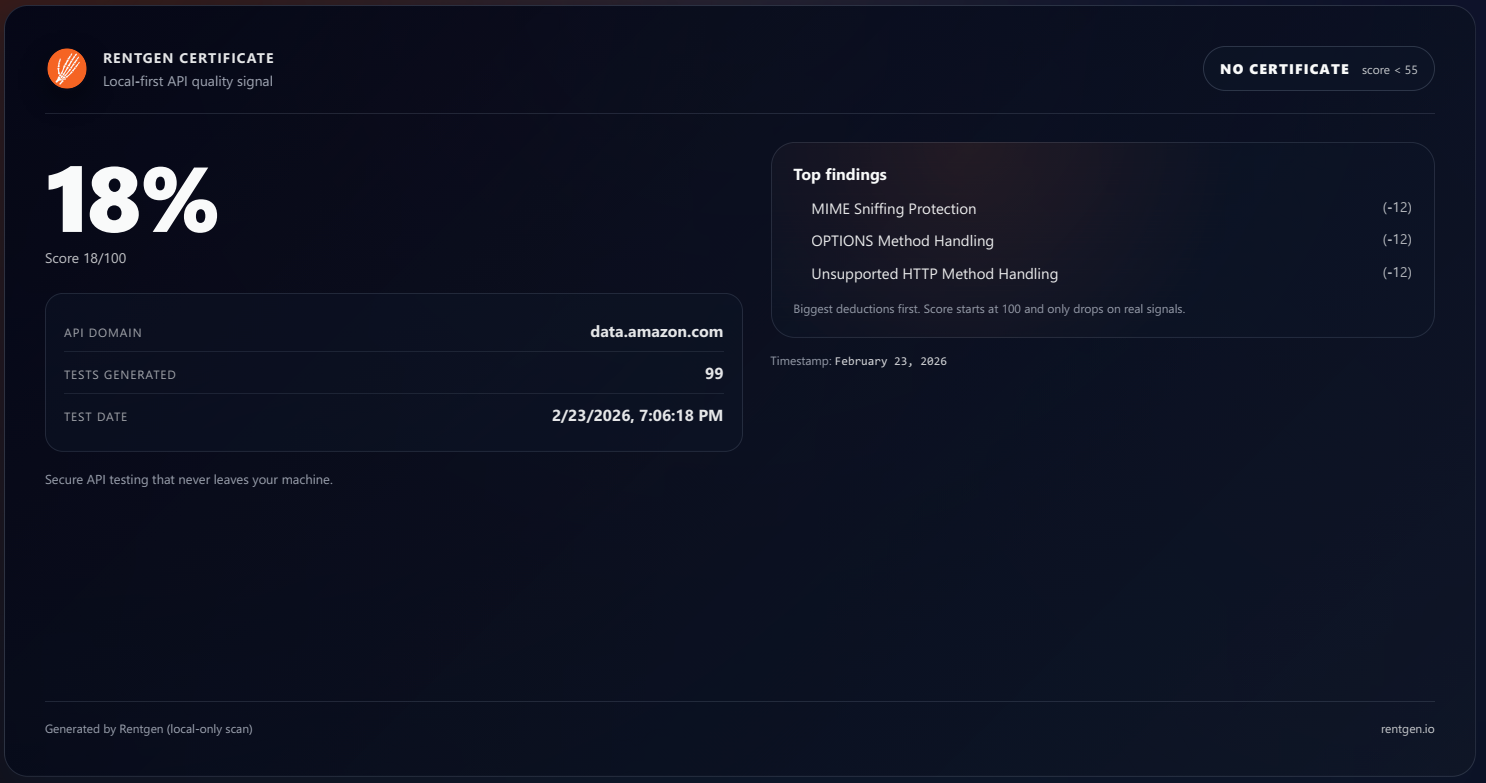
This endpoint received a 16 / 100 Rentgen certificate score — one of the lowest scores recorded in recent case studies.
The score reflects inconsistent status semantics, edge-layer leakage, and late-stage validation handling.
Conclusion
Large systems do not typically fail catastrophically. They degrade gradually through contract drift, semantic inconsistency, and infrastructure layering mismatches.
This case demonstrates how structural API signals can be identified in minutes without custom test scripts.
Rentgen operates before traditional test automation — exposing protocol-level issues early in the development lifecycle.
Automation before automation.
